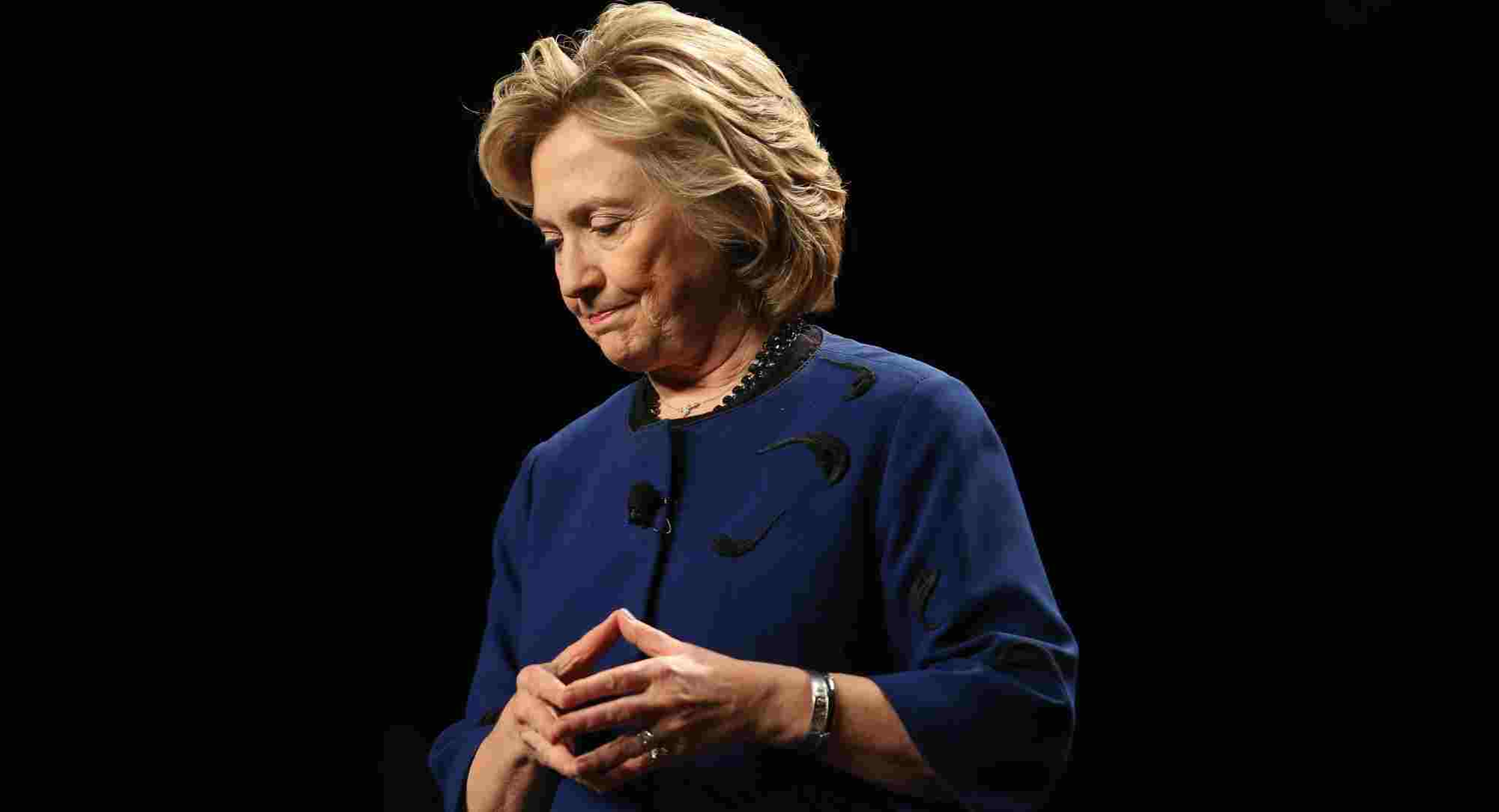
You have no doubt heard about Hillary Clinton's email case during the US presidential election in 2016. This controversy focuses on her personal email server. She used her personal email address to communicate sensitive information.
Timeline
In March 2015, following an article in The New York Times, she was targeted for the use of a private email server as part of her position as Secretary of State. Sending sensitive information via email is considered illegal by the US government.
In July 2016, the FBI, through its director James Comey, released the findings of the investigation. He accused her of "extreme carelessness" in using her personal email server to exchange information classified as "defense secret". He also added that "any reasonable person in the position of Mrs. Clinton should have known that an unprotected server could not host classified information."
In December 2016, the CIA targeted individuals linked to the Russians who transmitted information to WikiLeaks from hacked emails.
The consequences
The information that is exchanged by email leaves a lot of traces. There are items sent, items deleted, and items received. It is therefore impossible for an email server to be a real fortress, it is more than evident that this one leaves traces.
Let's take our servers in the cloud, for example, which are administered by people we do not know and who could, if they are malicious, read the contents of your emails that pass on their servers.
There are also companies like Google (Gmail) or Microsoft (Hotmail) who read your email to target you for advertising. But what do they do with the sensitive information they collect in your emails?
Email servers make backup copies. So even if you delete items that have been backed up, a copy of your email exists somewhere.
If you use encrypted email software, it's a good start, but what if you need to communicate with someone who does not use your software? It's impossible to exchange sensitive information with this person.
If both parties use the software, what happens if someone is physically in front of your computer and opens your software? Oh yes! They can read its content.
This is just the tip of the iceberg. It is therefore necessary to protect the sensitive information that is intended to be kept confidential.
The Safe Solution
An email server keeps the data you sent, regardless of whether it's a government, banking, yours, or whatever. It keeps track of any emails sent through the sent or deleted items, not to mention the backup copies.
Using Secure Exchanges technology to communicate sensitive information via email, sent items, like those received, will leave no trace. Since the content of the message is encrypted in your mailbox and the message is self-destructing after reading, nobody can read its content.
Using the Outlook plugin, the information sent with Secure Exchanges is encrypted before it is sent to the Secure Exchanges server. Reading of their content is therefore impossible, whether by the FBI, the CIA, CSIS, hackers, governments, Google, or antispam. Only the recipient can read the contents of the message, and the message can only be read once.
Once the information is consumed, all trace is destroyed. Secure Exchanges is completely independent: you can use it to send to any email server and it requires no software to be opened by your recipient.
Try Secure Exchanges for free and secure your confidential exchanges.
Start free trial →